Feb 28, 2013
Hacking Micromax 400R (Mi-Fi)
Hacking means making things usable. For me most of the times its possible by creating stuff but sometimes have to break stuff. Today I hacked at a software just to get the functionality out as needed.Let me tell you the story in breaf -
Yesterday I bought a Micromax 400R (Mi-Fi), Its a great device and cheap too ( Got just for 2450INR ). The MMX 400R is wireless router and Wi – Fi hotspot. Can be used to share 2G-3G dataplan over Wi-Fi for max 5 devices.
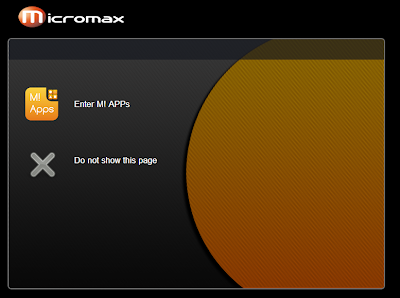
It was working well at start, but it started showing annoying ads when opening new web pages. For example if I am opening google.com, It redirects to 192.168.1.1/ads.html?url=http://google.com and ask you to "Enter M! APPs" or "Do not show this page". Every-time Have to click "Do not show this page".
Was something like this:-
I was exploring things, all the settings but found nothing to disable this ad. MMX 400R have a feature of "SD Card Sharing", Card can be accessed in browser by opening http://192.168.1.1 and choosing "Advance settings"-"Sharing"-"Sharing"
Buy exploring all the Ajax-calls I found that I can
1. View file list of a location using this call -
http://192.168.1.1/cgi-bin/ajax.cgi?which_cgi=ajax_get_file_list&pram=DIR_PATH 2. Can download file using this call - http://192.168.1.1/cgi-bin/export_file.cgi?get_file_path=DIR_PATH/FILE_NAME&get_file_name=FILE_NAME
2. Can create folder by using this call
http://192.168.1.1/cgi-bin/ajax.cgi?which_cgi=ajax_creat_folder&creat_current_folder_dir=DIR_PATH&lc_folder_name=FOLDER_NAME
3. Delete file or folder by using
http://192.168.1.1/cgi-bin/ajax.cgi?which_cgi=ajax_delete_file&file_op_name=DIR_OR_FILE_PATH
4. Upload or overwrite file, sending POST [multipart/form-data] request using these parameters current_folder_dir( value should be "longcheer_w>DIR_PATH>") lc_upfile ( type="file" File)
I tried and found that by using DIR_PATH as "/../../../mnt/resource/webpage" you can view, download or edit [ By uploading/overwriting ] all the scripts, files working at http://192.168.1.1/
I downloaded ads.html, as Its simple HTML/JS file, edited it so it can automatic redirect to the url without clicking on "Do not show this page".
Check this link for more info https://gist.github.com/OSConsumer/6548433
Try editing the cgi-scripts on your own risk.
Happy Hacking.
By : Motyar+ @motyar